Understanding Tor and VPN: An Overview
In today’s digital world, online privacy and security are of utmost importance. Two popular tools that are often used to protect one’s online privacy are Tor and VPN.
Tor, short for “The Onion Router,” is a free and open-source software that enables anonymous communication by routing internet traffic through a global network of volunteer nodes, making it difficult for anyone to track the user’s online activities.
On the other hand, VPN, or Virtual Private Network, is a service that creates an encrypted tunnel between the user’s device and the internet, providing a secure and private connection.
Both Tor and VPN have their unique features and limitations. Tor is known for its strong anonymity and ability to access the dark web, but it can be slower due to the multiple hops it takes to route traffic.
VPN, on the other hand, offers faster speeds and is commonly used to bypass geo-restrictions, but may require trust in the VPN provider.
When it comes to choosing between Tor and VPN, it largely depends on the user’s specific needs and threat model. Tor may be preferable for those who require maximum anonymity and are willing to sacrifice some speed, while VPN may be suitable for those who prioritize speed and convenience but may not require the same level of anonymity.
In conclusion, Tor and VPN are both valuable tools for protecting online privacy, but they have different functionalities and trade-offs. Understanding the basics of Tor and VPN can help users make informed decisions about which tool is best suited for their individual needs.
How Tor Works: Advantages and Limitations
Tor, short for “The Onion Router,” is a widely used software that allows users to browse the internet anonymously. Tor works by routing internet traffic through a network of volunteer-operated servers, or nodes, which are distributed across the globe.
This process encrypts the traffic multiple times, creating layers of protection, similar to an onion, hence the name “The Onion Router.”
One of the key advantages of Tor is its strong anonymity, as it makes it difficult for anyone, including ISPs and governments, to track a user’s online activities.
One of the key advantages of Tor is its strong anonymity, as it makes it difficult for anyone, including ISPs and governments, to track a user’s online activities. Tor also enables access to the dark web, which contains websites not indexed by traditional search engines. However, Tor does have some limitations, such as potential slowdowns due to the multiple hops the traffic takes and the possibility of encountering malicious nodes that may compromise user privacy.
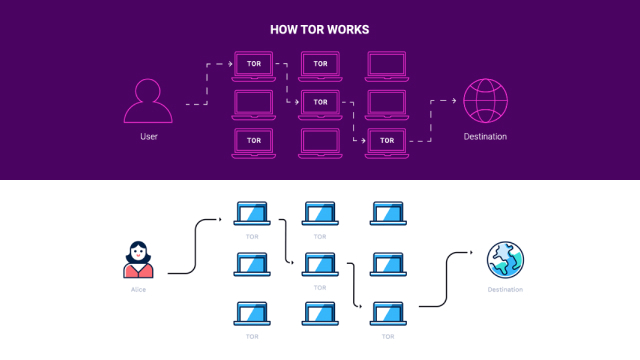
In summary, Tor provides a powerful tool for online anonymity, but it also has its limitations. Understanding how Tor works, its advantages, and limitations can help users make informed decisions about its usage and ensure they are using it safely and effectively for their privacy needs.
How VPN Works: Pros and Cons
A Virtual Private Network (VPN) is a technology that creates a secure and encrypted connection between a user’s device and the internet, allowing them to browse the web with increased privacy and security.
VPNs work by routing a user’s internet traffic through a remote server operated by the VPN provider, masking the user’s IP address and encrypting their data.
There are several advantages to using a VPN:
- Protecting Privacy: Hides users’ online activities from ISPs.
- Data Encryption: Prevents eavesdropping by encrypting data.
- Bypassing Restrictions: Enables access to geo-restricted content.
However, VPNs also have some potential downsides, such as potential slowdowns due to the extra step of routing traffic through a remote server and the reliance on the trustworthiness of the VPN provider.
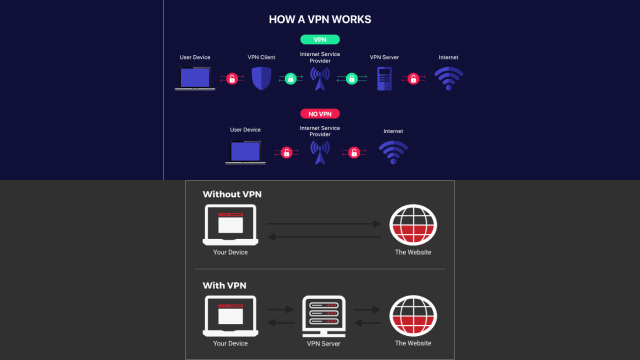
In conclusion, VPNs offer enhanced privacy and security for online activities, but they also come with some trade-offs. Understanding how VPNs work and their pros and cons can help users make informed decisions about their usage and choose a VPN service that meets their specific needs.
Key Differences Between Tor and VPN
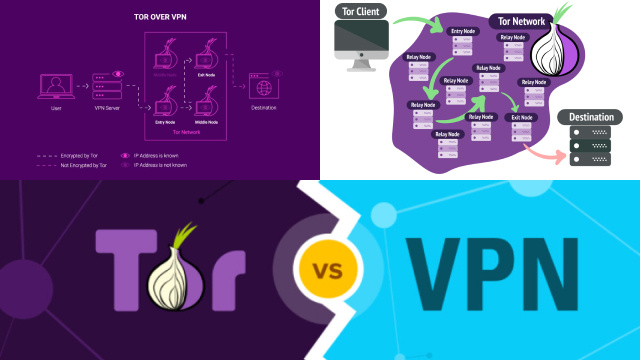
Tor and VPN are two popular technologies used for enhancing online privacy and security, but they have distinct differences. Tor, short for The Onion Router, is a decentralized network that routes internet traffic through a series of volunteer-operated servers, making it difficult to trace the origin of the traffic. On the other hand, a Virtual Private Network (VPN) is a service that encrypts a user’s internet traffic and routes it through a remote server operated by the VPN provider.
The main differences between Tor and VPN include the way they route traffic, the level of encryption, and the types of activities they are best suited for. Tor provides a higher level of anonymity as traffic passes through multiple relays, but it may be slower due to the number of hops. VPNs, on the other hand, typically offer faster speeds and are more suitable for general internet browsing, streaming, and online gaming.
In summary, Tor and VPN are distinct technologies with different approaches to enhancing online privacy and security. Understanding their key differences can help users choose the appropriate tool based on their specific needs and requirements.
Which Is Better in 2026? Tor or VPN?
Tor and VPN are two popular technologies used to enhance online privacy and security, but they have distinct differences:
- Tor (The Onion Router): A decentralized network that routes internet traffic through a series of volunteer-operated servers, making it difficult to trace the origin of the traffic.
- VPN (Virtual Private Network): A service that encrypts a user’s internet traffic and routes it through a remote server operated by the VPN provider.
Key Differences:
- Traffic Routing: Tor uses multiple relays for anonymity, while VPN routes traffic through a single remote server.
- Anonymity vs. Speed: Tor provides higher anonymity but may be slower due to multiple hops. VPN offers faster speeds, making it ideal for general browsing, streaming, and gaming.
In summary, Tor and VPN take different approaches to online privacy and security. Understanding these differences can help users choose the best tool for their specific needs.
Which Is Better in 2026? Tor or VPN?
As we navigate the evolving landscape of online privacy and security in 2025, the choice between Tor and VPN remains subjective and depends on individual needs. Both technologies have unique advantages and limitations:
- Tor: A decentralized network that routes traffic through multiple relays, offering a higher level of anonymity. However, it may have slower speeds due to the number of hops.
- VPN: Provides faster speeds and encryption, making it suitable for general internet browsing, streaming, and online gaming.
Choosing Between Tor and VPN:
- Tor: Ideal for those who prioritize anonymity, such as whistleblowers or journalists.
- VPN: Better suited for users seeking faster speeds and broader online access.
In conclusion, the decision between Tor and VPN in 2025 depends on individual preferences and requirements. Understanding the features of each technology is essential to choosing the one that best aligns with your privacy and security needs.
Considerations for Choosing Tor or VPN
When protecting your online privacy and security, choosing between Tor and VPN requires careful consideration.
- Tor:
- A decentralized network known for its strong anonymity.
- Ideal for users who prioritize hiding their online activities.
- May have slower speeds due to multi-hop routing.
- VPN:
- Offers faster speeds and encryption.
- Suitable for general internet use, streaming, and online gaming.
- Masks your IP address and encrypts your data, protecting your activities from prying eyes.
Factors to Consider:
- Level of Anonymity: Tor is better for maximum anonymity.
- Speed Requirements: VPN is preferable for faster speeds and broader online access.
- Specific Use Case: Match the tool to your privacy and performance needs.
Ultimately, the choice between Tor and VPN depends on your individual preferences and requirements. Understanding the features of each technology is essential for making an informed decision.
Using Tor and VPN Together: Pros and Cons
Combining Tor and VPN can provide an additional layer of privacy and security for online activities, but it’s essential to understand the pros and cons:
Advantages of Using Tor and VPN Together
- Increased Anonymity: Tor hides your IP address, while VPN encrypts your data, making it harder to trace your online activities.
- Bypassing Restrictions: The combination can help bypass censorship and access geo-restricted content.
Potential Downsides
- Decreased Internet Speeds: Multiple layers of encryption and routing may result in slower connection speeds.
- Complexity: Managing both technologies simultaneously can require technical expertise and configuration.

In conclusion, using Tor and VPN together can offer enhanced privacy and security, but it’s important to weigh the benefits against the potential drawbacks. It’s crucial to understand the technical aspects and limitations of each technology and carefully consider your specific needs and requirements before deciding to use Tor and VPN in combination.
Conclusion: Making the Right Choice for Your Online Privacy
In today’s digital world, protecting your online privacy is essential. Choosing between Tor and VPN depends on your specific needs and risk tolerance:
- Tor: A decentralized network that provides strong anonymity but may have slower speeds and limited access to certain websites.
- VPN: Offers encryption and faster speeds but relies on a trusted third-party server for routing.
Factors to Consider
- Threat Model: Evaluate the level of risk you face and the privacy you require.
- Online Activities: Determine your priorities, such as accessing restricted content or maintaining maximum anonymity.
- Legal and Ethical Considerations: Use Tor and VPN responsibly and in compliance with applicable laws.
In conclusion, The right choice for online privacy depends on individual needs and preferences. Research, assess the advantages and limitations of each technology, and choose wisely to protect your privacy and security while navigating the digital landscape in 2025 and beyond.